Your Full Map To Github Recon And Leaks Exposure
Hello My Name Orwa Atyat
https://twitter.com/GodfatherOrwa
Iam Bug Bounty Hunter
I start bug bounty in 02–2020 With no any idea or any background In pentest but I like it
I know these writing came late but it’s late because i want put everything here for github and all for you keep these writ up with you as source in Github,
I always believed that sharing is caring, and i have been learning from multiple security researchers in the bug bounty field,
so i decided to share All what i Have in Github from recon And find leaks and found ends points I will share all my tips and dorks and how to use github manuily and by some tools
1- what we have to know about github
GitHub is a truly awesome service but it is unwise to put any sensitive data in code that is hosted on GitHub and similar services
Here we begin the first lesson
that Github is divided into 3 sections
((ORG Page — User Page — Github Page))

2- The Best words in dorking And GitHub dorking in my ways Tips Dorks And recon with my way
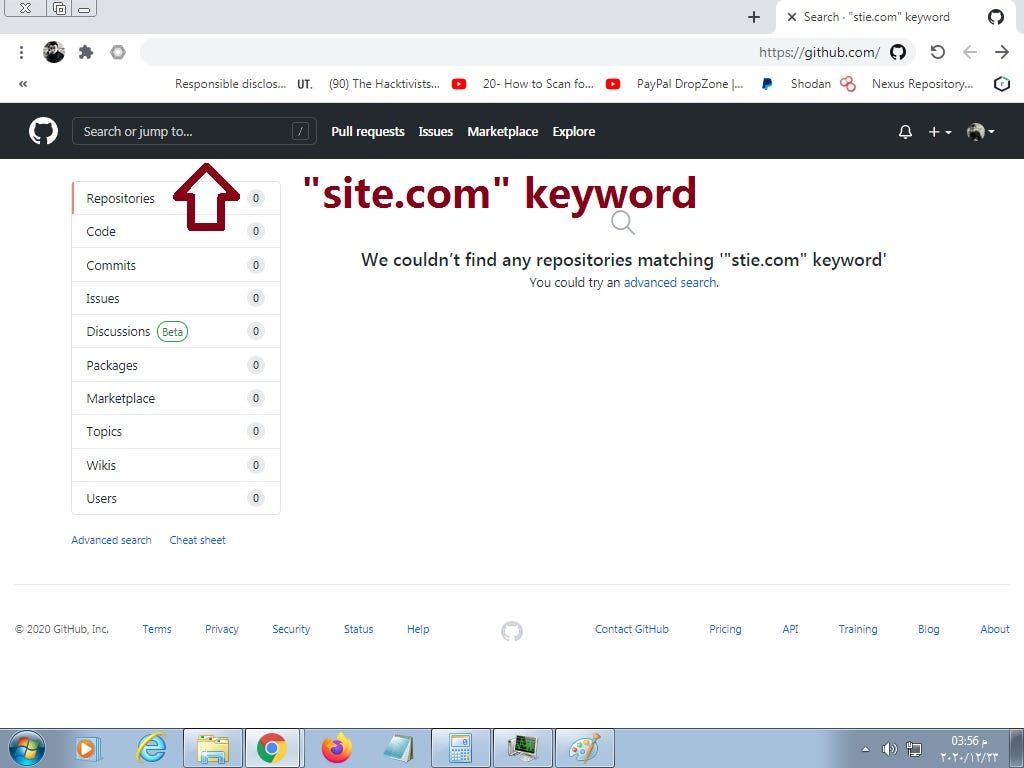
- “site.com” :
here you add your program you wanna search
((you can put “site.com”)) ((“sub.site.com”)) ((“site” only))
but site name like these ((site-site.com))and have these ((-)) the dork without ((“ “ ))
- Keyword
my Keyword that i like to use and i will add it with language that i like to use
Jenkins
OTP
oauth
authoriztion
password
pwd
ftp
dotfiles
JDBC
key-keys
send_key-keys
send,key-keys
token
user
login-singin
passkey-passkeys
pass
secret
SecretAccessKey
app_AWS_SECRET_ACCESS_KEY AWS_SECRET_ACCESS_KEY
credentials
config
security_credentials
connectionstring
ssh2_auth_password
DB_PASSWORD
— — — — — — — — — — — — — — — — — — -BASH — — — — — — — — — —
language:bash password
language:bash pwd
language:bash ftp
language:bash dotfiles
language:bash JDBC
language:bash key-keys
language:bash send_key-keys
language:bash send,key-keys
language:bash token
language:bash user
language:bash login-singin
language:bash passkey-passkeys
language:bash pass
language:bash secret
language:bash credentials
language:bash config
language:bash security_credentials
language:bash connectionstring
language:bash ssh2_auth_password
— — — — — — — — — — — — — — — — — — -PYTHON — — — — — — — — —
language:python password
language:python pwd
language:python ftp
language:python dotfiles
language:python JDBC
language:python key-keys
language:python send_key-keys
language:python send,key-keys
language:python token
language:python user
language:python login-singin
language:python passkey-passkeys
language:python pass
language:python secret
language:python credentials
language:python config
language:python security_credentials
language:python connectionstring
language:python ssh2_auth_password
the most lovely for me
password — passwd — pwd — secret — private — Ldap
why ???
because if i use keyword like secret
i can got all of these result
secret_key
secretkey
secret api
secret token
secret pass
secret password
aws secret
client secret
Etc….
these link have good dorks
https://github.com/techgaun/github-dorks/blob/master/github-dorks.txt
- Language:
if you have lot lot of codes and work in a Big program
you can dork with language
the best language i like
bash
python
ruby
java
so in dorking with language
just like these
“bugcrowd.com” password language:bash
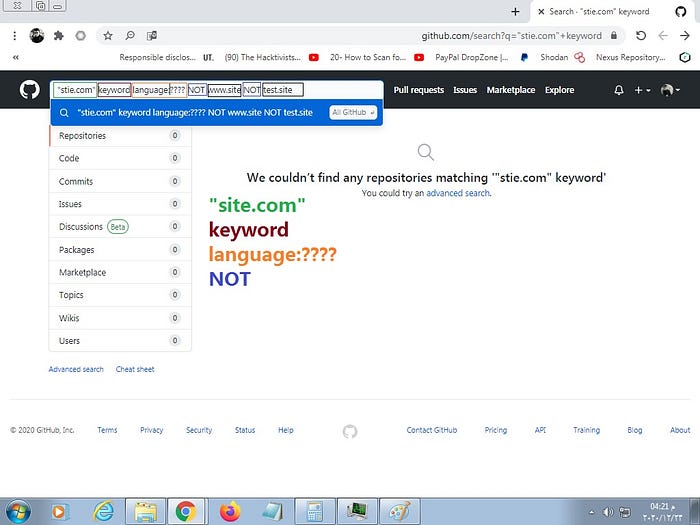
- NOT: **capital**
it’s a very important word
use for filter the result
FOR example
you wanna search for “bugcrowd.com”
and you have like 5K codes
When you browse through these codes
You find a code
like
www.bugcrowd.com
that is constantly being repeated and in a way that annoys you
now you can filter these code by use
“bugcrowd.com” NOT www.bugcrowd ((but in NOT dont add .com))
and you will got like 2K codes
after that you see When you browse through these codes
You find a code
like
test.bugcrowd.com
you can filter these code with the other one by use
“bugcrowd.com” NOT www.bugcrowd NOT test.bugcrowd
and you will got like 1K codes - The most big dork ever I use was for Paypal
that dork
“paypal” language:python password NOT sandbox.paypal NOT api.paypal NOT www.paypal NOT gmail.com NOT yahoo.com NOT hotmail.com NOT test
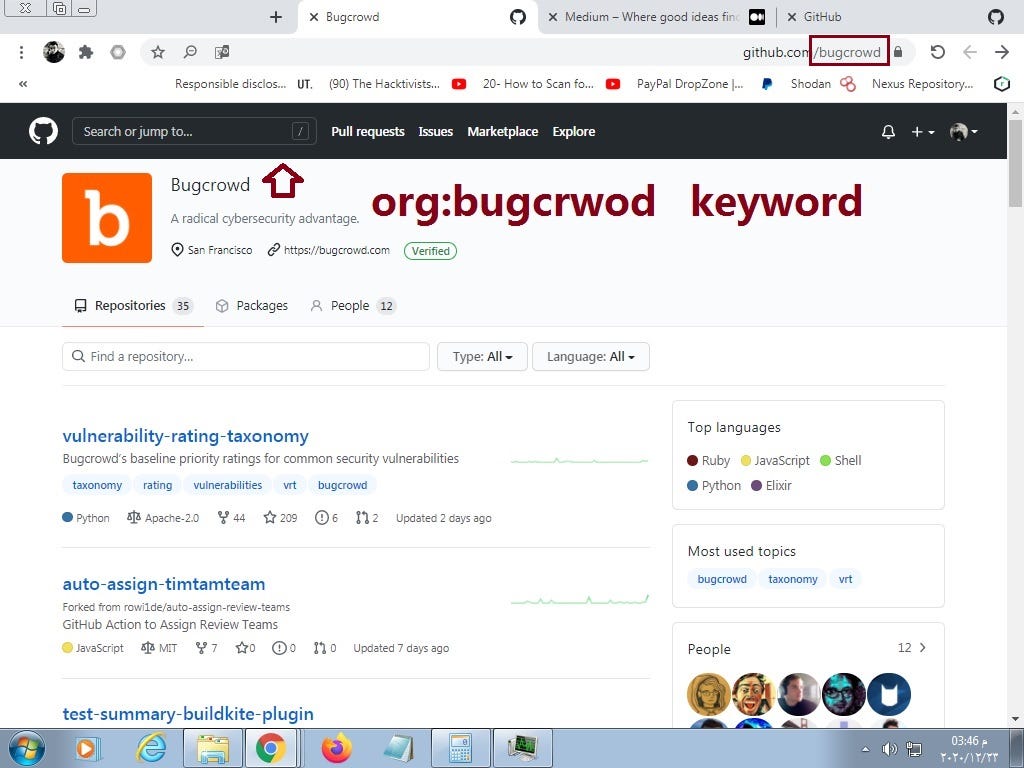
So now Examples
for Org
org:bugcrowd password NOT www.bugcrowd
for User
user:orwagodfather secret
for github page
“bugcrowd.com” language:python secret NOT www.bugcrowd
3- MY TIPS & WAYS & My advice
A:
now
if the program say
in scope:
bugcrowd.com
out of scope
blog.bugcrowd.com
think out of the box
the leaked data all the time in scope
so start search for evrything belong fo bugcrowd
make for your self your scope like these
inscop
*.bugcrowd.*
any domian belong for bugcrowd
B:
when you dorking
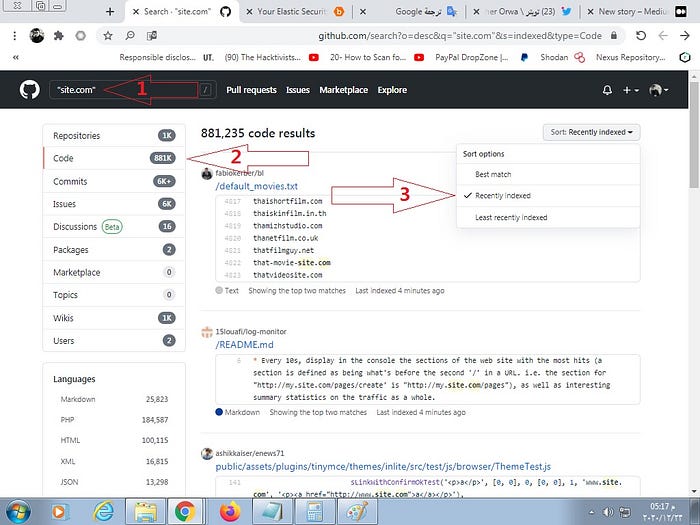
Always focus on the most recent date
You need fresh data Not old
I will repeat that: FOCUS ON THE DATE
YOU NEED FRESH DATA NOT OLD DATA
C:
and all the time if you found something for same user
check that user in linkedin if he work for these program or not
some employees hide that where they work in github but dont hide that from linkedin
the dork if you wanna check orwa if he work in bugcrowd that dork in google
orwa atyat bugcrowd linkedin
or
check orwa user search for some ends points or some info about orwa
by dork
user:orwagodfather linkedin
user:orwagodfather full name
user:orwagodfather https://
user:orwagodfather Ldap
and just like these do some recon like if you wanna know about some internal links in org you can do like these
org:bugcrowd https://
org:bugcrowd host:
sometimes you got some lnternal link
This link is for a special or important page
It is not protected by a username and password
Or it requires default credentials
like admin admin
or admin password
with these you have a full access and cool and easy P1 report
With these tips I guarantee you will find something
thats me
i don’t have mythology
i don’t have a leader
i think out the box
I follow Th3g3n3lman because thats man who make my good hunter with shearing all the stuff in twitter
i all the time collaborated with
https://twitter.com/waseyuddin and all thanks for these kind man
4- Some Github Good Tips from my reports
A:
Some companies rely on cloud services specially in that period for remote work, so when you look for credentials on github and similar services remember that examples:
“centrify.com” password
service-now.com password You can try send_keys keyword also.
B:
github+translate
if you search for leaks for Russian program
as example you can put the dork in Russian language
or if you search for user from Italy
you can put the dork in Italian language
that leads to good results
as my found in Russian language
host
user
pass
C:
good #github #Tips
“site.com" password or secret or any keyword
“target.atlassian” password or secret or any keyword
“target.okta” password or secret or any keyword
“corp.target" password or secret or any keyword
“jira.target" password or secret or any keyword
“target.onelogin” password or secret or any keyword
target.service-now password or secret or any keyword
sometime use these tips without any keyword
now i have lot of finds and good bounty
but if you see
i work manually because i like that
but i recommend by any tool
its will be these tool its vary vary good and helpful
https://github.com/obheda12/GitDorker
for these amazing man
https://twitter.com/obheda12
and you can read about in
https://medium.com/@obheda12/gitdorker-a-new-tool-for-manual-github-dorking-and-easy-bug-bounty-wins-92a0a0a6b8d5
Tom Edson did a thousand failed experiments,, But the thousand and one experiment was the lamp ,, So do not be afraid to submit a thousand reports,, every failed experiment is a step closer to success
now this my first write up so sorry and forgive me if i write something you not understand here
Dont forget check th3g3nt3lman Video about github
https://www.youtube.com/watch?v=l0YsEk_59fQ
and my next writup will be about the google dorking
i suggest you add these men
https://twitter.com/waseyuddin
amazing smart and i cant hunt without him
thanks all
orwa atyat
https://twitter.com/GodfatherOrwa




![How i was able to get critical bug on google by get full access on [Google Cloud BI Hackathon]](https://miro.medium.com/v2/resize:fit:679/1*9tkWLuPd9NaPTmWCsa1nGA.png)


